By submitting this form, you consent to Qualys' privacy policy
Email or call us at 1 (800) 745-4355
Our SSPM tool helps you automate the process of managing your SaaS apps, including global settings, user privileges, licenses, files, and their security and compliance posture.
To secure your SaaS applications and prevent your confidential data from being exposed, you need continuous, end-to-end visibility of all your deployments.

Gain clarity and control of your SaaS stack by providing in-depth user and device visibility, data security insights, proactive posture monitoring, and automated remediation of threats - all from a single screen.
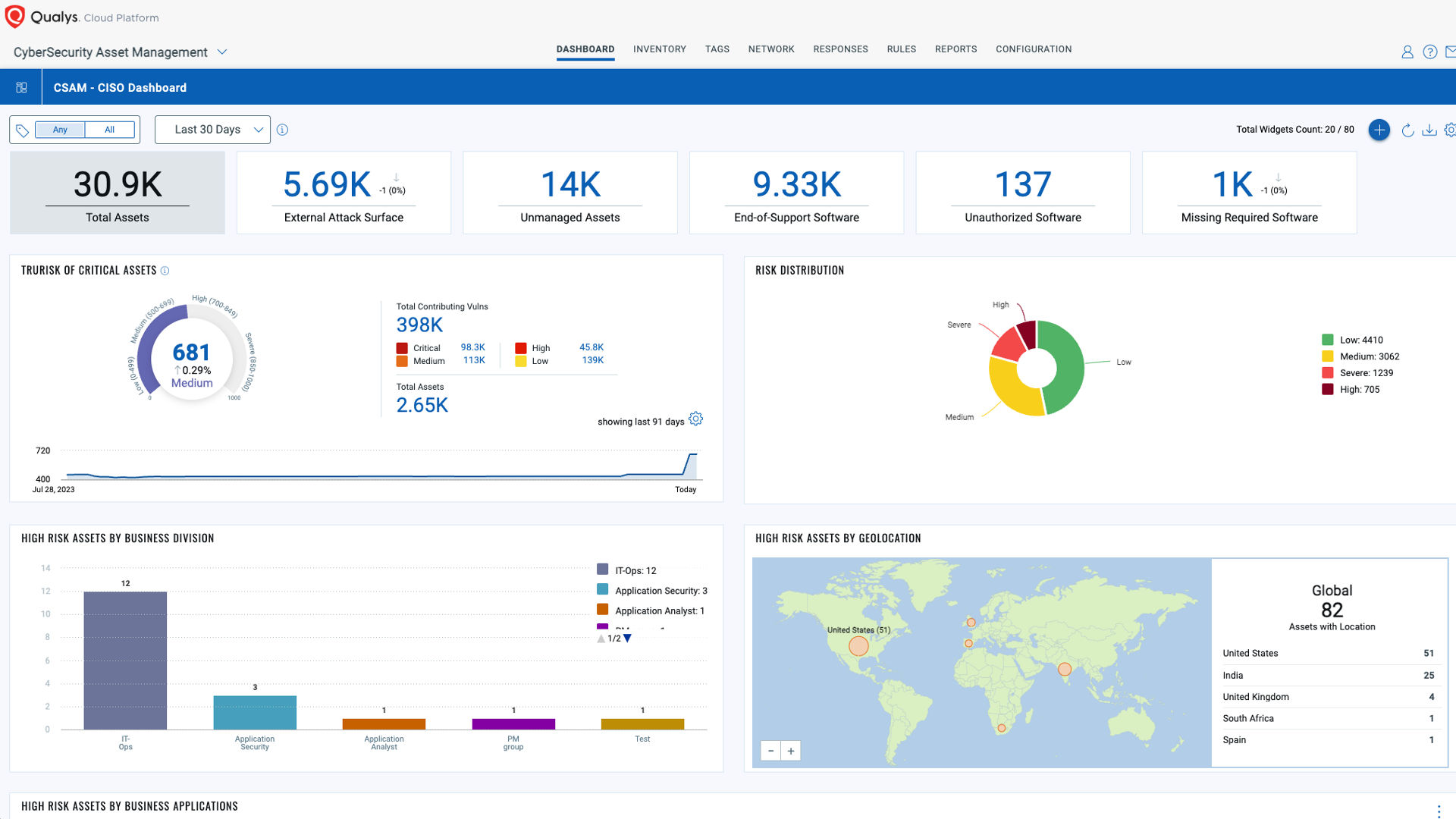
The Enterprise TruRisk Platform provides you with a unified view of your entire cyber risk posture so you can efficiently aggregate and measure all Qualys & non-Qualys risk factors in a unified view, communicate cyber risk with context to your business, and go beyond patching to eliminate the risk that threatens the business in any area of your attack surface.